Biometric attendance data security in Bangladesh is now one of the most important topics for businesses, schools, factories, and government offices. More and more places are using fingerprint or face scanners to track who comes to work. But with this new technology comes a big question: Is the data safe?
This guide will walk you through everything you need to know. We will cover how biometric systems work, what the law says, how to keep data safe, and what to do if something goes wrong. Whether you run a small office or a large factory, this guide is for you.
Common Biometric Methods Used in Bangladesh
Before we talk about security, let us first understand what types of biometric systems people use in Bangladesh.
Fingerprint Recognition Systems
Fingerprint systems are the most common type in Bangladesh. The device scans your finger and saves a digital copy. Every time you come to work, you place your finger on the scanner. The system checks if your fingerprint matches the saved one.
These systems are affordable and easy to use. That is why so many factories, offices, and schools use them.
Facial Recognition Systems
Facial recognition systems use a camera to scan your face. You just look at the camera and the system records your attendance. No touching is needed.
These systems are becoming more popular in Bangladesh, especially after COVID-19 when people wanted touch-free options.
RFID and Biometric Hybrid Systems
Some organizations use a mix of RFID cards and biometric scans. You tap your card and then scan your finger or face. This adds an extra layer of protection because two things need to match.
Multi-Modal Biometric Systems
Multi-modal systems use more than one biometric method at the same time. For example, they might scan both your fingerprint and your face. This makes it very hard for anyone to trick the system.
Legal Framework Governing Biometric Data in Bangladesh
Bangladesh does not yet have a single law just for biometric data. But there are laws that do apply to how organizations collect and store personal data.
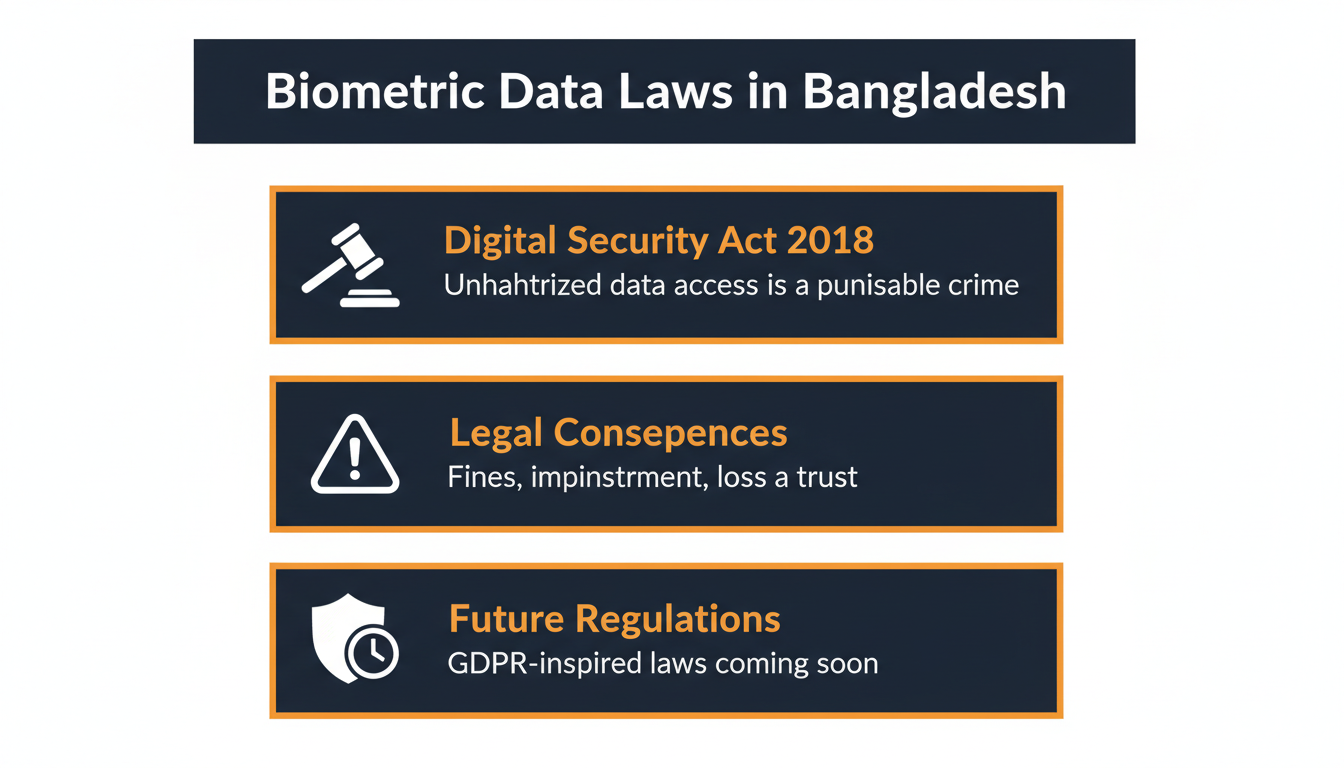
Digital Security Act 2018 and Its Implications
The Digital Security Act 2018 is the main law in Bangladesh that deals with digital data and cybercrime. Under this law, accessing someone’s personal data without permission is a crime. Sharing or misusing digital data can lead to heavy fines or even prison time.
If your organization collects fingerprint or face data and someone steals or leaks that data, this law applies. Organizations need to take this seriously.
Legal Consequences of Data Breaches and Mismanagement
If biometric data is leaked or misused, the consequences can be serious. The organization can face legal action. Leaders can be personally held responsible. The company can also lose the trust of employees and clients.
Courts in Bangladesh are starting to pay more attention to digital data crimes. This trend will grow in the coming years.
Emerging Data Protection Regulations and Future Policies
Bangladesh is working on new data protection rules. These new rules will be similar to international standards like the GDPR used in Europe. Once these rules come into effect, organizations that collect biometric data will have stricter rules to follow.
It is smart to start following good data protection practices now, before the new laws arrive.
Data Privacy and Employee Rights in Bangladesh
When a company collects an employee’s fingerprint or face scan, that employee has rights. Organizations must respect those rights.
Employee Consent and Transparency Requirements
Before collecting biometric data, organizations must get clear permission from each employee. This is called informed consent. Employees should know:
• What data is being collected
• Why it is being collected
• How long it will be kept
• Who can access it
This should be explained in simple language, not legal jargon. Employees should sign a consent form.
Ethical Use of Biometric Data in the Workplace
Biometric data should only be used for the purpose for which it was collected. If you collect fingerprint data for attendance, you should not use it for anything else without permission.
Employees should also be able to ask what data is stored about them. If an employee leaves the company, their biometric data should be deleted.
Legal Risks of Unauthorized Data Access and Misuse
Accessing biometric data without permission is not just unethical; it is also illegal under the Digital Security Act 2018. Organizations must keep a clear record of who can access the data and when they accessed it.
If an employee or manager looks at biometric data without a valid reason, that is a violation. Organizations must have strict rules about who is allowed to access this data.
Key Security Features of Biometric Attendance Systems
A good biometric system does not just scan fingers or faces. It also protects the data it collects. Here are the main security features to look for.
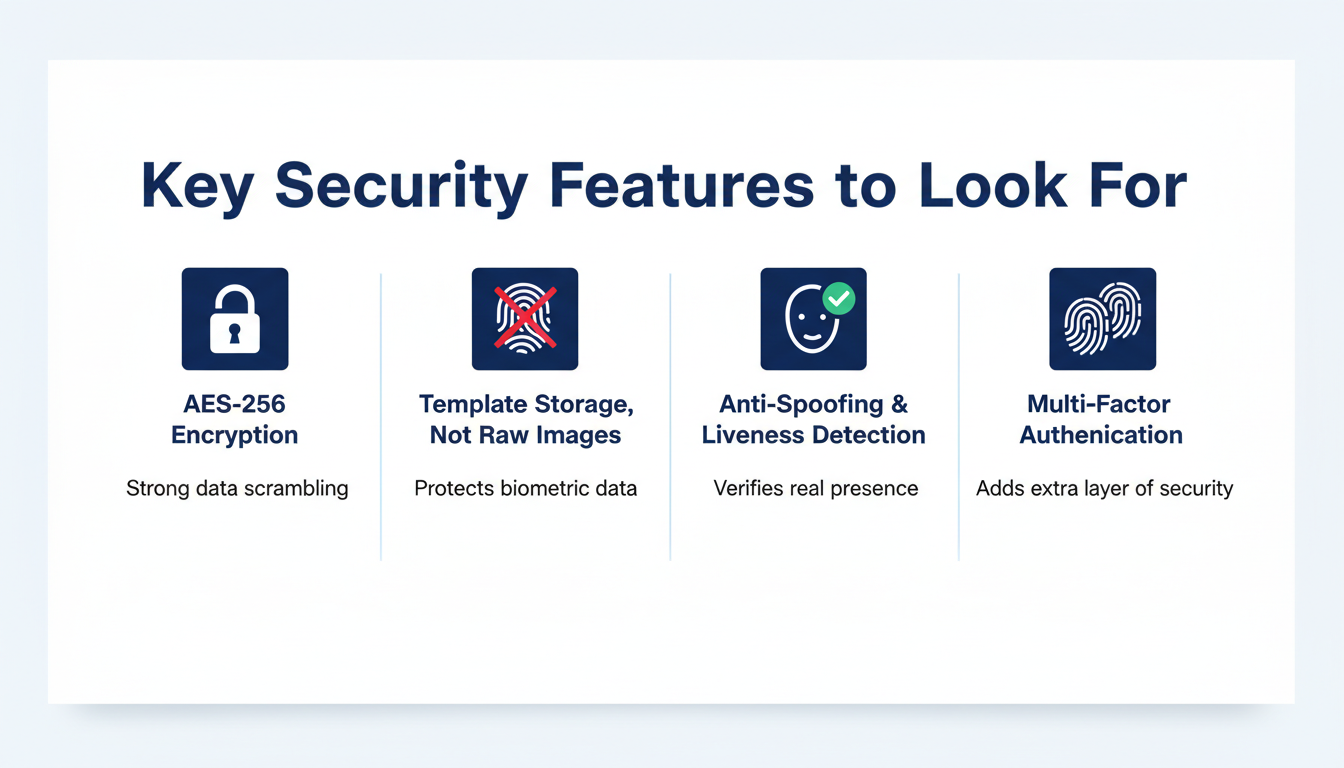
Encrypted Storage and Banking-Grade Security Standards
Encryption means that the data is turned into a secret code. Even if someone steals the data, they cannot read it without the key.
Good biometric systems use the same level of encryption that banks use. This is called AES-256 encryption. When you are buying a biometric system, ask if it uses this standard.
Use of Biometric Templates Instead of Raw Data
A good system does not save your actual fingerprint image. Instead, it saves a mathematical version called a template. This template cannot be turned back into a real fingerprint image.
This means even if someone steals the template, they cannot use it to copy your fingerprint. This is a very important safety feature.
Multi-Modal Authentication for Enhanced Protection
Using more than one type of biometric check makes the system much harder to trick. Some systems also add a PIN or password on top of the biometric scan.
This is called multi-factor authentication, and it is one of the best ways to protect your system.
Anti-Spoofing Technologies: Fake Finger and Presentation Attack Prevention
Some people try to trick biometric systems using fake fingers made of silicone or printed photos of faces. Modern devices can detect these tricks. This is called anti-spoofing or liveness detection.
The device checks if the finger is real and alive. It checks if the face is a real person and not a photo. Always choose devices that have this feature.
Data Storage and Deployment Models
Where you store biometric data matters a lot. There are two main options.
Cloud-Based vs On-Premise Biometric Systems
Cloud-based systems store data on servers managed by a company outside your organization. This is convenient because you can access the data from anywhere. But you must trust the cloud provider to keep the data safe.
On-premise systems store data on servers inside your own building. You have full control. But you are also fully responsible for keeping it safe.
For small businesses in Bangladesh, cloud-based systems are often easier to manage. For large organizations or government offices, on-premise may be better.
Data Localization and Storage Compliance Considerations
Some laws require that certain types of data must be stored inside the country. This is called data localization. Bangladesh is moving toward these kinds of rules.
If you use a cloud provider, make sure they can store your data in Bangladesh or at least in a country with strong data protection laws.
Secure Data Transfer Between Attendance and HR Systems
Biometric attendance data is often connected to payroll and HR software. Every time data moves from one system to another, there is a risk of it being stolen.
Always make sure data is encrypted during transfer. Use secure connections. Ask your software provider how they protect data when it moves between systems.
Integration of Security with HR and Payroll Systems
When biometric attendance systems connect with HR and payroll software, the risk of data leaks increases. Good integration security is very important.
Risks in API and Software Integrations
APIs are the tools that let two software systems talk to each other. If an API is not properly protected, it can be an easy way for hackers to get in.
Always make sure the APIs used by your biometric and HR systems are tested for security. Ask your software provider how they protect their APIs.
Best Practices for Secure System Integration
Use only trusted software from reputable providers. Always use encrypted connections when systems talk to each other. Regularly check if any unauthorized connections have been made.
Limit how much data is shared between systems. Only share what is absolutely needed.
Role-Based Access Control in Integrated Environments
Not everyone in your organization needs to see biometric data. Use role-based access control, which means each person can only see the data they need for their job.
For example, the HR manager might need to see attendance records. But the payroll officer only needs the total hours worked. The system should be set up so each person only sees what is needed.
Real-World Security Risks and Breach Scenarios
Understanding the risks is the first step to avoiding them.
Common Cyber Threats Targeting Biometric Systems
Hackers use many methods to attack biometric systems. These include:
• Phishing attacks to steal login credentials
• Malware that records data silently
• Network attacks that intercept data as it moves
• Brute force attacks that try many passwords until one works
Organizations in Bangladesh must be aware of these threats and have defenses in place.
Insider Threats and Unauthorized Access Risks
Not all threats come from outside. Sometimes the danger is inside the organization. An employee with access to the system might misuse it for personal reasons.
This is called an insider threat. It is one of the hardest risks to manage. Strong access controls and activity logs can help detect and prevent this.
Hypothetical Breach Scenarios in the Bangladeshi Context
Imagine a garment factory in Dhaka that uses a fingerprint attendance system. If a hacker breaks into the system, they could access the fingerprints of thousands of workers. Unlike a password, you cannot change your fingerprint. That data is lost forever.
Or consider a bank in Chittagong where an IT staff member copies the biometric data of managers. That person could use that data to create fake identities or commit fraud.
These scenarios are not just stories. They can happen in real life. Organizations must prepare before a breach happens, not after.
Best Practices for Securing Biometric Attendance Systems
Here are the most important steps every organization in Bangladesh should follow.
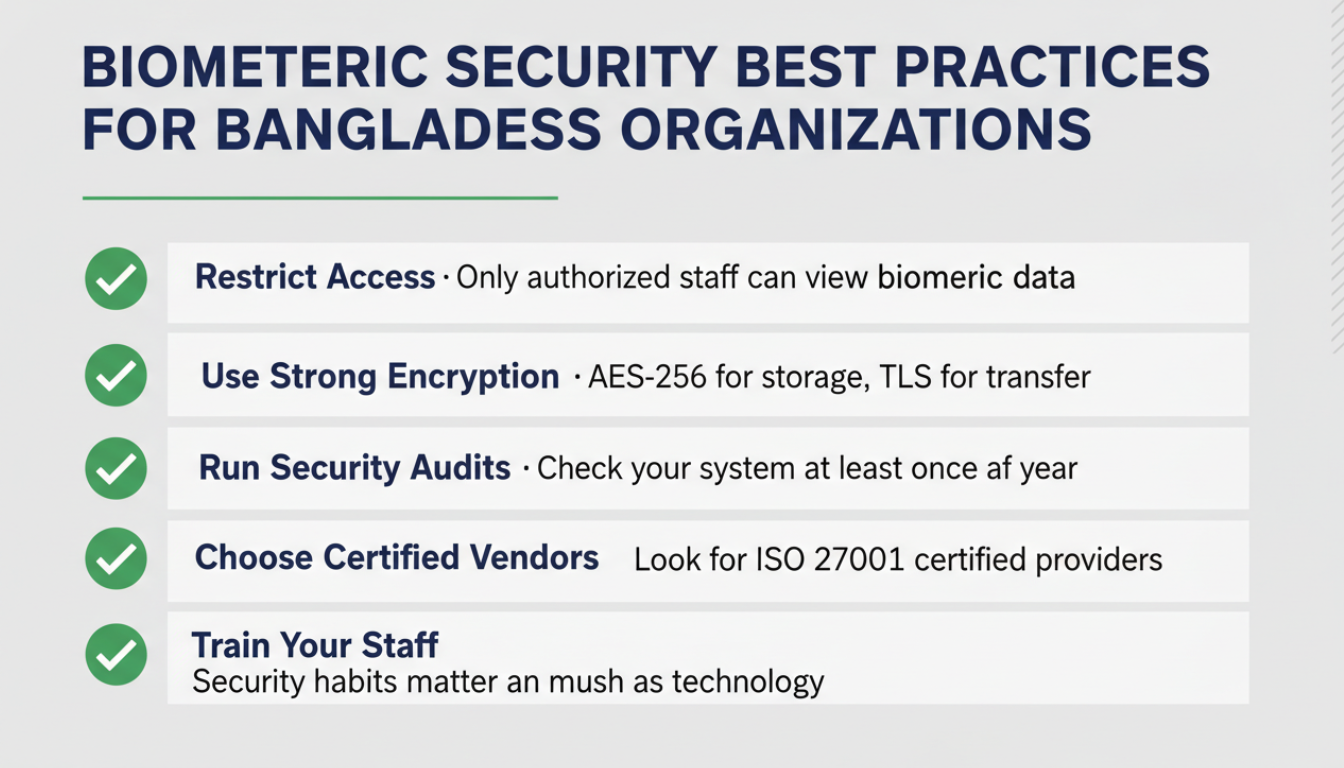
Restricting Access to Authorized Personnel Only
Only the people who truly need access should have it. Keep a list of who has access and review that list regularly. Remove access immediately when someone leaves the company.
Implementing Strong Encryption Protocols
Use AES-256 encryption for stored data. Use TLS encryption for data that is being transferred. Ask your vendor if they support these standards before you buy.
Regular Security Audits and System Updates
Check your system regularly for weaknesses. Update your software whenever new versions come out. Old software often has security holes that hackers can use.
Hire a security expert once a year to check your system if possible. This is called a security audit.
Building Internal Data Security Policies and Compliance Culture
Create simple, clear rules about how biometric data should be handled in your organization. Train all staff on these rules. Make sure everyone knows that misusing biometric data is a serious matter.
Security is not just about technology. It is also about people and habits.
Vendor Selection and Security Evaluation
Choosing the right vendor is one of the most important decisions you will make.
Security Certifications and Compliance Standards to Look For
When choosing a biometric system provider, look for these certifications:
• ISO 27001 (information security management)
• CE marking (safety standards for electronic devices)
• FCC certification (for electronic safety)
These certifications show that the product has been tested and meets international standards.
Key Questions to Ask Biometric System Providers
Before buying, ask these questions:
• How is the biometric data stored and encrypted?
• Where is the data stored (local or cloud)?
• Do you use biometric templates or raw images?
• What anti-spoofing technology do you use?
• What happens to the data if I stop using your service?
• Do you provide regular software updates?
A good vendor will be happy to answer all these questions clearly.
Choosing Reliable and Secure Hardware Providers in Bangladesh
In Bangladesh, there are many vendors selling biometric devices. Not all of them offer the same level of security. Choose vendors who have a track record, offer after-sales support, and can provide clear answers to your security questions.
If you are looking for a trusted option, you can explore the biometric attendance system solutions available in Bangladesh to find providers who take security seriously.
Cost vs Security Considerations
Many organizations in Bangladesh try to save money by buying cheaper biometric systems. This can be a costly mistake.
Balancing Budget Constraints with Data Protection Needs
A cheaper device might not have proper encryption or anti-spoofing features. It might save data in raw image format instead of templates. It might not get regular security updates.
Set a budget that allows you to buy a device that meets at least the basic security standards. Think of it as an investment, not a cost.
Hidden Costs of Weak Security Implementation
If a cheap system leads to a data breach, the real costs can be very high. You might have to pay legal fines. You might lose client contracts. You might spend a lot of money fixing the problem.
The cost of a data breach is almost always much higher than the cost of buying a secure system in the first place.
Long-Term ROI of Investing in Secure Biometric Systems
A secure biometric system saves money in the long run. It reduces time theft, improves payroll accuracy, and builds employee trust. It also protects you from legal trouble.
Think of security as a feature, not an extra expense.
Biometric Systems vs Traditional Attendance Systems
How do biometric systems compare to the older ways of tracking attendance?
Security Advantages Over Manual and Card-Based Systems
Manual registers can be faked. Someone can sign in for another person. Punch cards and RFID cards can be shared or stolen.
Biometric systems are much harder to trick. You cannot give someone else your fingerprint or your face. This makes attendance records far more accurate and trustworthy.
Remaining Risks Compared to Non-Biometric Methods
Biometric systems are not perfect. If the data is not stored securely, it can be stolen. And unlike a password or card, you cannot replace your fingerprint if it is compromised.
This is why strong data security is so important when using biometric systems.
When Biometric Systems Are the Right Choice
Biometric systems are the right choice when you need high accuracy, want to eliminate buddy punching, and are willing to invest in proper data security. They work best when combined with strong policies and trained staff.
Limitations of Biometric Systems and Risk Mitigation
Every technology has limits. Knowing them helps you prepare better.
Potential Vulnerabilities in Biometric Technologies
Biometric systems can be fooled by high-quality fakes if they lack liveness detection. Database breaches can expose templates. Network attacks can intercept data during transfer.
No system is 100% safe. But with the right measures, the risks can be greatly reduced.
How to Reduce Risk Through Policy and Technology
Use devices with anti-spoofing features. Store only templates, not raw images. Encrypt all data. Use role-based access control. Run regular security audits.
Combine technology with strong internal policies for the best protection.
Importance of Continuous Monitoring and Staff Training
Security is not a one-time job. You must keep watching for threats. Check system logs regularly. Train staff on security rules at least once a year.
When staff understand why security matters, they are more likely to follow the rules.
Incident Response and Data Breach Management
Even with the best security, breaches can happen. Having a plan ready is very important.
Steps to Take Immediately After a Biometric Data Breach
If a breach happens, act fast. Here is what to do:
1. Identify what data was accessed or stolen
2. Disconnect affected systems from the network
3. Preserve evidence for investigation
4. Notify your IT team and management immediately
5. Contact a cybersecurity expert if needed
Time matters. The faster you act, the less damage there will be.
Creating an Internal Incident Response Plan
Write down exactly what your organization will do if a breach happens. Assign roles. Who will lead the response? Who will talk to employees? Who will contact the authorities?
Practice the plan, so everyone knows what to do. A drill once a year can make a big difference.
Notifying Authorities and Affected Employees
Under the Digital Security Act 2018, organizations may be required to report a breach to the relevant authorities. Affected employees should also be informed as soon as possible.
Be honest. Tell employees what happened and what you are doing about it. Trust is hard to rebuild once it is lost.
Future Trends in Biometric Security in Bangladesh
The world of biometric security is changing fast. Here is what to expect in the coming years.
AI-Based Threat Detection and Behavioral Biometrics
Artificial intelligence is being used to spot unusual behavior in biometric systems. For example, if someone logs in from an unusual location or at an unusual time, the system can flag it for review.
Behavioral biometrics goes even further. It studies how a person types, moves their mouse, or holds their phone. This can be used as an extra layer of identity verification.
Advancements in Device-Level Security
Newer biometric devices are built with security features directly in the hardware. This means the device itself can detect and block attacks. Sensors are getting better at detecting fake fingers and faces.
As prices come down, these advanced devices will become more available to small and medium businesses in Bangladesh.
Evolution of Regulatory and Security Standards in Bangladesh
Bangladesh is moving toward stronger data protection laws. International standards like ISO and GDPR-inspired regulations will shape how biometric data is managed.
Organizations that prepare now will have an easier time when the new laws arrive. Start building good security habits today.
FAQs on Biometric Attendance Data Security in Bangladesh
Is Biometric Data Safe to Use in Bangladesh?
Yes, biometric data can be used safely in Bangladesh if the right security measures are in place. Organizations must use encrypted systems, train staff, and follow the rules under the Digital Security Act 2018. Choosing a trusted vendor is also very important.
Can Biometric Data Be Hacked or Stolen?
Yes, like any digital data, biometric data can be hacked if it is not properly protected. This is why encryption, anti-spoofing, and regular security audits are so important. Good systems store biometric templates instead of raw images, which reduces risk even if a breach happens.
What Happens If Biometric Data Is Leaked?
If biometric data is leaked, the people affected cannot change their fingerprints or faces. The damage can be long-lasting. The organization responsible may face legal action under the Digital Security Act 2018, lose client trust, and have to pay for the cost of fixing the breach.
How Do I Choose a Secure Biometric Attendance System?
Look for systems with AES-256 encryption, liveness detection, template-based storage, and regular software updates. Ask the vendor about their security certifications. For trusted options in Bangladesh, you can check out reliable biometric attendance systems that follow proper security standards.
What Are the Legal Obligations for Employers Collecting Biometric Data?
Employers must get clear consent from employees before collecting their biometric data. They must store it securely, use it only for its stated purpose, and delete it when it is no longer needed. The Digital Security Act 2018 applies to any misuse of this data.
Conclusion
Biometric attendance data security in Bangladesh is not just a technical issue. It is a legal, ethical, and business issue. As more organizations adopt fingerprint and facial recognition systems, the need to protect that data becomes more urgent.
Key Takeaways for Organizations in Bangladesh
• Always get employee consent before collecting biometric data
• Use encrypted systems and store templates, not raw images
• Know your legal obligations under the Digital Security Act 2018
• Choose vendors who take security seriously
• Have a clear incident response plan ready
Final Recommendations for Secure Biometric Adoption
Start with a trusted system. Train your staff. Review your security regularly. And stay updated on new laws and standards as they develop.
Biometric technology is powerful. When used responsibly, it can make your organization more efficient and more secure. The key is to handle the data with the same care you would want someone to handle your own personal information.
If you are ready to take the next step, explore the biometric attendance system options available in Bangladesh and choose a solution that puts security first.








